27 posts tagged “cookies”
2024
In 2021 we [the Mozilla engineering team] found “samesite=lax by default” isn’t shippable without what you call the “two minute twist” - you risk breaking a lot of websites. If you have that kind of two-minute exception, a lot of exploits that were supposed to be prevented remain possible.
When we tried rolling it out, we had to deal with a lot of broken websites: Debugging cookie behavior in website backends is nontrivial from a browser.
Firefox also had a prototype of what I believe is a better protection (including additional privacy benefits) already underway (called total cookie protection).
Given all of this, we paused samesite lax by default development in favor of this.
2021
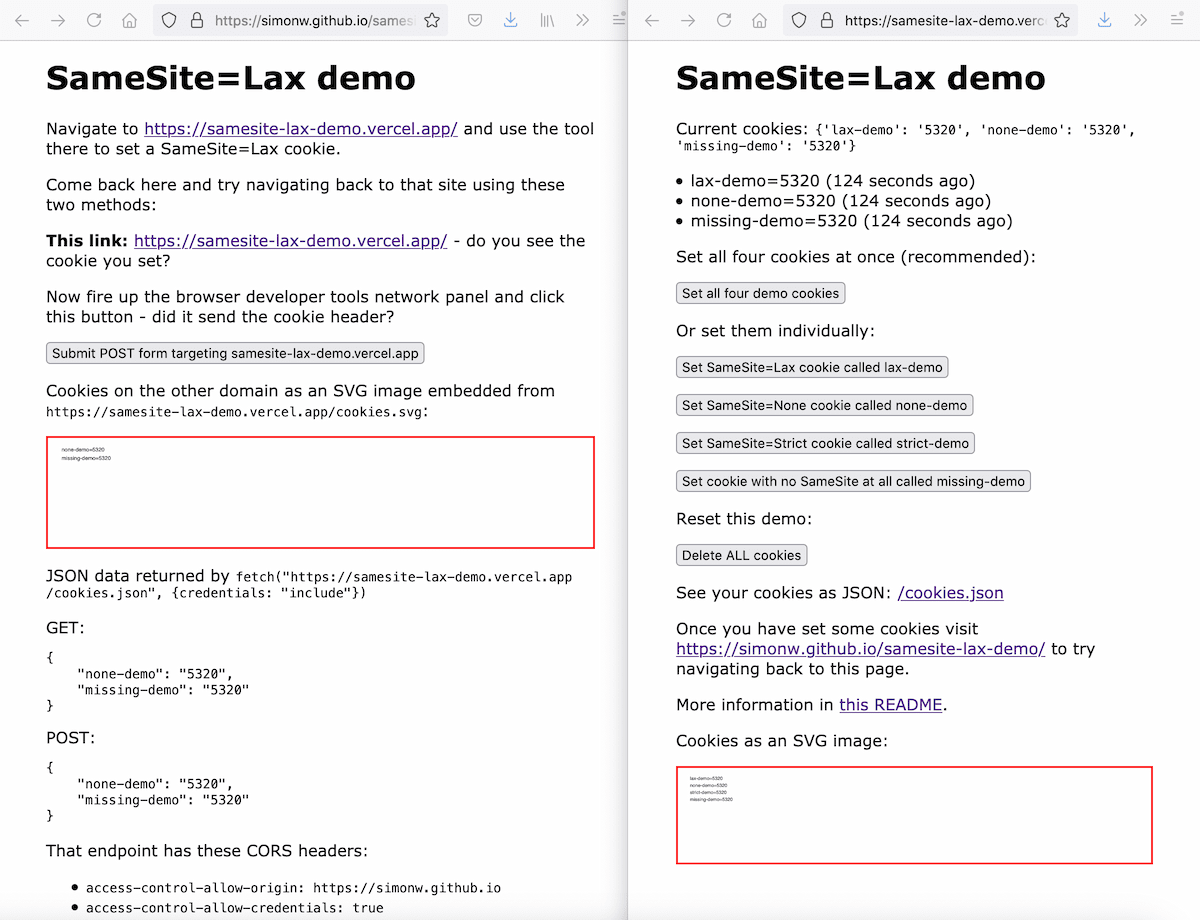
Exploring the SameSite cookie attribute for preventing CSRF
In reading Yan Zhu’s excellent write-up of the JSON CSRF vulnerability she found in OkCupid one thing puzzled me: I was under the impression that browsers these days default to treating cookies as SameSite=Lax, so I would expect attacks like the one Yan described not to work in modern browsers.
2020
At GitHub, we want to protect developer privacy, and we find cookie banners quite irritating, so we decided to look for a solution. After a brief search, we found one: just don’t use any non-essential cookies. Pretty simple, really. 🤔
So, we have removed all non-essential cookies from GitHub, and visiting our website does not send any information to third-party analytics services.
Tip for changing cookie subdomains: change the cookie name too. This is a really useful tip I hadn’t encountered before. If you make a change to the way cookies are configured—changing the cookie domain or path for example—it’s a good idea to change the name of the cookie as well. If you don’t change the cookie name you’ll see weird behaviour for users who have previously had the cookie set using the older configuration. This definitely explains bugs I’ve seen in the past. Filing this tip away for future cookie-related development work.
Weeknotes: datasette-auth-existing-cookies and datasette-sentry
Work on Datasette Cloud continues—I’m tantalizingly close to having a MVP I can start to invite people to try out.
[... 701 words]Come version 80, any cookie without a SameSite attribute will be treated as "Lax" by Chrome. This is really important to understand because put simply, it'll very likely break a bunch of stuff. [...] The fix is easy, all it needs is for everyone responsible for maintaining any system that uses cookies that might be passed from an external origin to understand what's going on. Can't be that hard, right? Hello? Oh...
2018
Cookies-over-HTTP Bad (via) Mike West from the Chrome security team proposes a way for browsers to start discouraging the use of tracking cookies sent over HTTP—which represent a significant threat to user privacy from network attackers. It’s a clever piece of thinking: browsers would slowly ramp up the forced expiry deadline for non-HTTPS cookies, further encouraging sites to switch to HTTPS cookies while giving them ample time to adapt.
2012
Can you mark items on a website as ’unread’ without cookies?
It’s not very exciting, but CSS will let you set different styles for visited vs unvisited links and the technique has worked reliably since the mid 1990s.
[... 44 words]2010
Firesheep (via) Oh wow. A Firefox extension that makes sniffing for insecured (non-HTTPS) cookie requests on your current WiFi network and logging in as that person a case of clicking a couple of buttons. Always possible of course, but it’s never been made easy before. Private VPNs are about to become a lot more popular.
Facebook’s Instant Personalization: An Analysis of Fundamental Privacy Flaws (via) Oh FFS. “Instant Personalization” means you visit one of Facebook’s “partner websites” and Facebook instantly tells them your full identity and gives them access to full Facebook connect functionality—without you performing any action other than visiting the site. This will not end well.
Internet Explorer Cookie Internals (FAQ). Grr... IE 6, 7 and 8 don’t support the max-age cookie argument, forcing you to use an explicit expiry date instead. This appears to affect the cache busting cookie pattern, where you set a cookie to expire in 30 seconds for any user who posts content and use the presence of that cookie to skip caches and/or send their queries to a master instead of slave database. If you have to use expires, users with incorrect system clocks may get inconsistent results. Anyone know of a workaround?
2009
Negative Cashback from Bing Cashback (via) Some online stores show you a higher price if you click through from Bing—and set a cookie that continues to show you the higher price for the next three months. It’s unclear if this is Bing’s fault—comments on Hacker News report that Google Shopping sometimes suffers from the same problem (POST UPDATED: I originally blamed Bing for this).
Django ponies: Proposals for Django 1.2
I’ve decided to step up my involvement in Django development in the run-up to Django 1.2, so I’m currently going through several years worth of accumulated pony requests figuring out which ones are worth advocating for. I’m also ensuring I have the code to back them up—my innocent AutoEscaping proposal a few years ago resulted in an enormous amount of work by Malcolm and I don’t think he’d appreciate a repeat performance.
[... 1,674 words]Adding signing (and signed cookies) to Django core. I’ve been increasing my participation in Django recently—here’s my proposal for adding signing and signed cookies to Django, which I’d personally like to see ship as part of Django 1.2.
You Deleted Your Cookies? Think Again (via) Flash cookies last longer than browser cookies and are harder to delete. Some services are sneakily “respawning” their cookies—if you clear the regular tracking cookie it will be reinstated from the Flash data next time you visit a page.
Towards a Standard for Django Session Messages. I completely agree that Django’s user.message_set (which I helped design) is unfit for purpose, but I don’t think sessions are the right solution for messages sent to users. A signed cookie containing either the full message or a key referencing the message body on the server is a much more generally useful solution as it avoids the need for a round trip to a persistent store entirely.
2008
Integrating Facebook Connect with Django in 15 minutes. Django authentication middleware that calls the Facebook REST API using a cookie set by Facebook Connect and checks if that person is your Facebook friend. Despite most of the magic happening on the server you still need Facebook’s JavaScript to set that cookie in the first place.
Django snippets: Sign a string using SHA1, then shrink it using url-safe base65. I needed a way to create tamper-proof URLs and cookies by signing them, but didn’t want the overhead of a full 40 character SHA1 hash. After some experimentation, it turns out you can knock a 40 char hash down to 27 characters by encoding it using a custom base65 encoding which only uses URL-safe characters.
Major Update to Prism (via) Mozilla’s site-specific browser tool can now use separate profiles (and hence separate cookie jars) for each instance, making it an excellent tool for protecting yourself against CSRF vulnerabilities in the web applications you rely on.
2007
Fluid. Another site-specific browser toolkit for OS X (Leopard only), from Todd Ditchendorf. Again, it’s not clear if this does the Right Thing and creates separate cookie jars for every application.
Site-specific browsers and GreaseKit. New site-specific browser tool which lets you include a bunch of Greasemonkey scripts. For me, the killer feature of site-specific browsers is still cookie isolation (to minimise the impact of XSS and CSRF holes) but none of the current batch of tools advertise this as a feature, and most seem to want to share the system-wide cookie jar.
Currently WebRunner applications share cookies with other WebRunner applications, but not with Firefox. WebRunner uses its own profile, not Firefox's profile. There is a plan to allow WebRunner applications to create their own, private profiles as well.
IE vulnerability allows cookie stealing. Full exploit against the same-domain cookie origin policy, so malicious sites can steal cookies from elsewhere. Avoid using IE until this is patched.
IE and 2-letter domain-names (via) IE won’t let you set a cookie on XX.YY, where YY is anything other than .pl or .gr. Other browsers have better exception lists.
There's an unfortunate side-effect to altogether eliminating the sub-domain name from your site URLs [...] Every cookie you may want to set for that site will automatically "bleed" down to all sub-domain-based websites you might want to add later.
Ubuntu sugar cookies (via) Different coloured dough is used to bake the Ubuntu logo in to the cookies themselves, kind of like making sushi rolls.
2003
Thirty five year old cookies
I’m finding myself slightly confused about the Google backlash washing around the blogosphere, which is summarised quite well by Gavin Sheridan. Most of the arguments against using Google unsurprisingly centre around privacy issues, in particular the “35 year cookie”. I was under the impression that cookies could only be set for a maximum of a year, but having checked Netscape’s Cookie Specification and RFC 2965 it appears I was mistaken.
[... 566 words]