Entries tagged security, xss
Filters: Type: entry × security × xss × Sorted by date
Weeknotes: Page caching and custom templates for Datasette Cloud
My main development focus this week has been adding public page caching to Datasette Cloud, and exploring what custom template support might look like for that service.
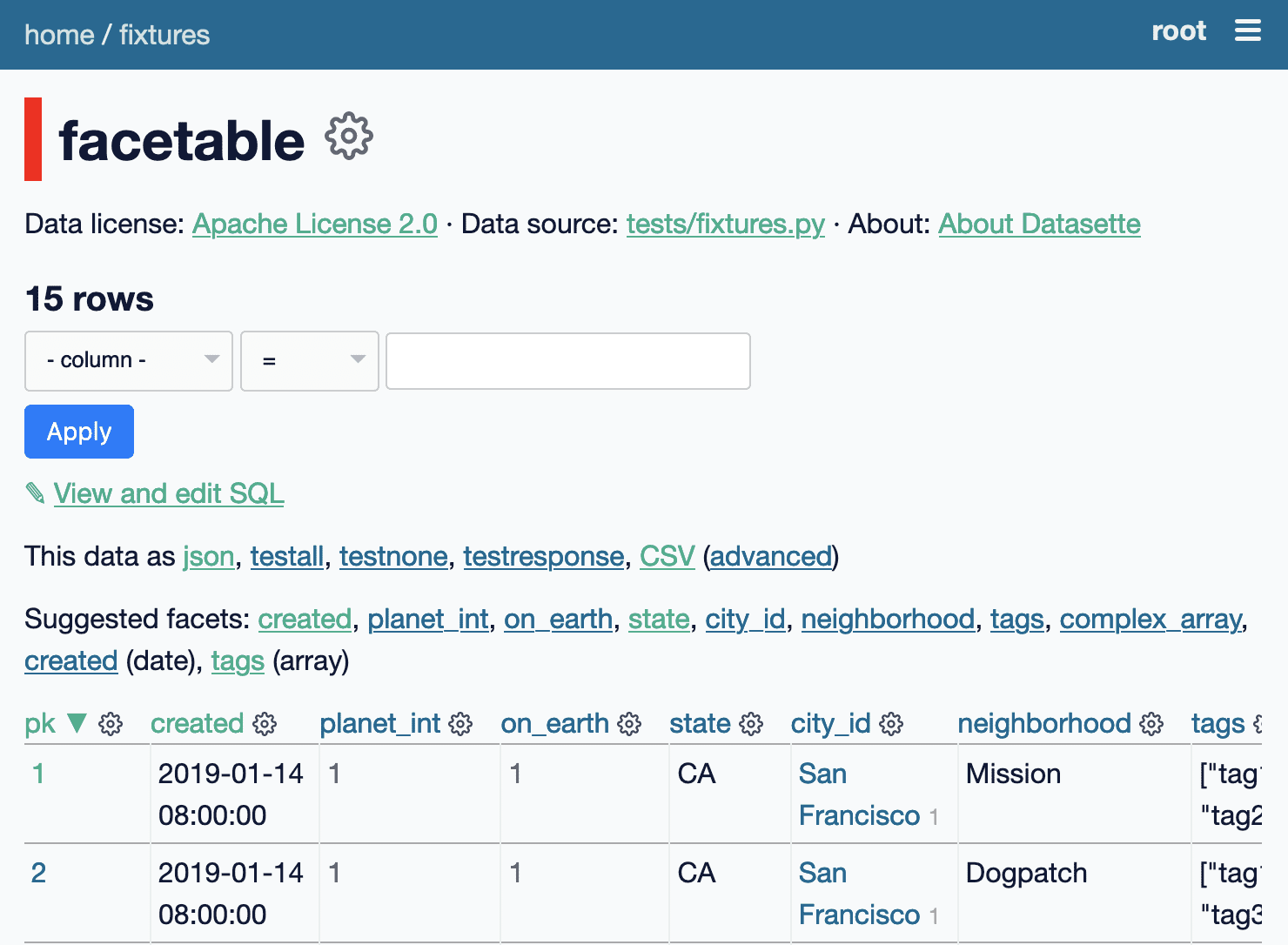
[... 924 words]Datasette 0.51 (plus weeknotes)
I shipped Datasette 0.51 today, with a new visual design, plugin hooks for adding navigation options, better handling of binary data, URL building utility methods and better support for running Datasette behind a proxy. It’s a lot of stuff! Here are the annotated release notes.
[... 2,020 words]What are the best practices to avoid XSS and SQL Injections attacks (platform agnostic)?
Input validation is, in my opinion, a red herring. Sure—if you ask the user for an integer or date you should make sure they entered one before attempting to save it anywhere or use it for processing, but injection attacks often involve text fields (e.g. names, or comments posted on Quora) and validating those on input is a recipe for banning “Tim O’Reilly” from ever creating a proper profile on your site!
[... 316 words]Why are XSS attacks spreading like fire these days?
XSS attacks are common and easy, and crop up all the time. What’s new is that the number of people who are aware of the potential for XSS worms has increased hugely, so when an XSS does crop up in something popular there’s a much higher chance of someone turning it in to a worm (as happened with Twitter the other day).
[... 96 words]Designing for a security breach
User account breaches are inevitable. We should take that in to account when designing our applications.
[... 545 words]The Register hit by XSS
Here’s a nasty one: popular tech news site The Register was hit on Saturday by the Bofra exploit, a nasty worm which uses an iframe vulnerability in (you guessed it) Internet Explorer to install nasty things on the victim’s PC. Where it gets interesting is that the attack wasn’t against the Register themselves; it came through their third party ad serving company, Falk AG.
[... 262 words]